VLANs are a feature of almost all managed network switchesWikipedia: A network switch (also called switching hub, bridging hub, and, by the IEEE, MAC bridge[1]) is networking hardware that connects devices on a computer network by using packet switching to receive and .... A managed switch will allow you to assign ports to VLAN groups. Devices in one VLAN will not be able to directly communicate with devices in another VLAN. In simple terms, creating VLANs is a bit like splitting a switch into multiple smaller switches.
Why would I buy an expensive managed switch when I could just buy multiple cheap unmanaged switches, I hear you ask. Well, a port can be assigned to multiple VLANs. If you wanted to, for example, break 192.168.0.1/24 (254 usable IP addresses) into 2 groups of 192.168.0.1-192.168.0.100 and 192.168.0.101-192.168.0.254 you could create 2 VLANs, one for devices in each IP range. You could then have an administrative terminal connected to a switch port which is in both VLANs. This administrative terminal can then access devices in both IP ranges.
So what is 802.1Q VLAN tagging? Well, it allows a single port to access multiple VLANs, even if devices in each VLAN are in a different IP subnet. For example, if your network had two departments one which used 192.168.0.1/24 and the other which used 10.1.1.1/24, you could create two VLANs as described above. You could then create a 802.1Q VLAN tagged port on the switch and connect a device such as an administrative computer or a router into it. You would then configure the administrative computer or router to assign it 2 IP addresses (for example 192.168.0.100 and 10.1.1.100) and associate each IP with the correct VLAN. Every packet of data that is sent from the router to the switch would tell the switch which VLAN it is for (and visa versa).
Here is an example usecase for 802.1Q VLANs:
A switch has 3 VLANs on it…
- Ports 1-4 :: Internet facing devices such as the modem and servers
- Ports 5-14 :: Devices in the finance department
- Ports 14-20 :: Devices in the HR department
In ports 1-4 (VLAN1) we have connected the modem and a Linux server. These have public IP addresses in the 13.14.15.16/28 range. In ports 5-14 we have connected PCs in the finance department which have private IP addresses in the 192.168.1.0/24 range. In ports 14-20 we have devices in the HR department which have private IP addresses in the 10.0.1.0/24 range.
Port 21 is 802.1Q VLAN tagged with access to all 3 VLANs. Into this port, we have connected a router. This router has an IP address for each VLAN (192.168.1.1, 10.0.1.1 and 13.14.15.17). The router routes packets between the three VLANs to give private IPs access to the Internet, using NAT, as well as routing packets between the two private subnets to give the HR department access to files in the finance department and visa versa.
tl;dr
Can a device running DD-WRT which has 802.1Q capability use 3 unmanaged switches AS 1 managed switch with VLAN?
Instead of DD-WRT could PFsense box with 2 real interfaces? or PFsense box with 1 real interaces?
__need
I have home fios (fttp verizon). I currently only have one public ip address but I hope to purchase one additional — current packages are 1 or 5. The ISP router flavors both destroy sip quality; I am stuck with the less horrible westell router. I have a not too old dell optiplex to use as PFsense firewall/router with 2 real interfaces (intel pro 1000 pci-e) as it only has 2 pci-e 16x. I have a voip ATA. I do not use wifi. Occasionally I power a dd-wrt as AP for relatives who whine about no wifi and horrible AT&T data dead zones.
I want one public IP address for the voip ata (to avoid fiddling with nat rules). The other IP address for PFsense to NAT around to various numberous devices
vlan_1_guests
I want one group (vlan) to have only internet access and zero access to lan NFS shares. Rather than enable NFS authentication in ubuntu. Occasionally I would want to power a DD-WRT as AP for needy relatives who visit.
vlan_2
One vlan to have internet and lan NFS shares.
vlan_3_kids
One vlan to have anti-porn filtering and lan NFS shares; this third group will have PFsense rules (afaik) to require the dns resolvers set and disouraging various other circumventy tunneling (hamachi, ‘free’ vpn, stunnel), blocking p2p usenet, all http ssl, all chat other than xmpp or sip.
In our home we (I) don’t pay for sms for texting; we use xmpp or sip simple.
spare switch abundance
As various floors in the house have exapnded hardware count I’ve purchased larger unmanaged switches so I have some extra ones. I have no managed switches.
xmpp:matts@Jabber.me/otr (require otr)
sip:matts@ostel.co (zrtp or simple)
A VLANed managed switch is very similar to a set of unmanaged switches in all except the fact a single port cannot be in multiple VLANs.
As such, for your setup, your dd-wrt/pfsense router will need one physical interface per VLAN. On the topic of pfSense, I’ve had a lot of luck running it in production on the interface-rich X series routers – https://phil.lavin.me.uk/2013/03/installing-pfsense-on-a-watchguard-firebox-x550e-and-x750e/ – specifically an x750e which you can pick up on eBay for about £100.
Basically you would connect each physical interface of the router into a different switch and use those switches as connection points for individual networks. The rest of your setup should be conducted at the router. This isn’t totally ideal as you’ll lose the ability to use broadcast protocols because devices cannot be in multiple VLANs without routing.
It’s important not to confuse the LAN ports on cheaper routers with physical ports as these are typically just an inbuilt switch. DD-WRT can break these apart into untagged VLANs on some Broadcom based hardware but it’s a bit of a balls to do. See https://phil.lavin.me.uk/2012/10/creating-a-guest-wifi-with-802-1q-vlan-tagging-in-pfsense-and-dd-wrt/.
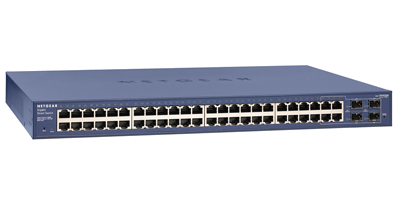
Another option is to get a managed switch. I can recommend the Netgear GS724T or GS748T (24 and 48 port models respectively) as cheap managed gigabit switches. If you’re going with the GS748T, try to find a v3 as the v1 have a design flaw – https://phil.lavin.me.uk/2011/12/netgear-gs748t-heatsink-pins-design-flaw/.
Phil